At the end of 2019, Quickbooks Online is deprecating their OAuth1 service in favor of using OAuth2. After December 17th, 2019, Quickbooks will be revoking all OAuth1 tokens and no new tokens will be granted. To avoid connection failures, you will need to migrate your OAuth1 QBO element instances to OAuth2.
Cloud Elements is happy to provide the following migration scripts that will handle this for you at this Github Link. Essentially, there are two scripts:
- the first to find all the OAuth1 QBO instances that need to be migrated
- the second to migrate those instances to OAuth2
You will need to supply the following pieces of information to the first script:
- User Secret
- Organization Secret
- Your Cloud Elements Environment (Staging or Prod)
You will need to supply the previous information into the second script, as well as:
- OAuth 2.0 Client Id associated with your OAuth 1.0 application
- OAuth 2.0 Client Secret associated with your OAuth 1.0 application
- List of instances procured by running the first script
Special Notes:
- The migration endpoint is /migrate-tokens
- In your header, you still need your full Auth Header which includes User+Organization+Element.
- In the payload, you want to include the following:
- {
"client_id": "XXXXX",
"client_secret": "XXXXX"
}
- {
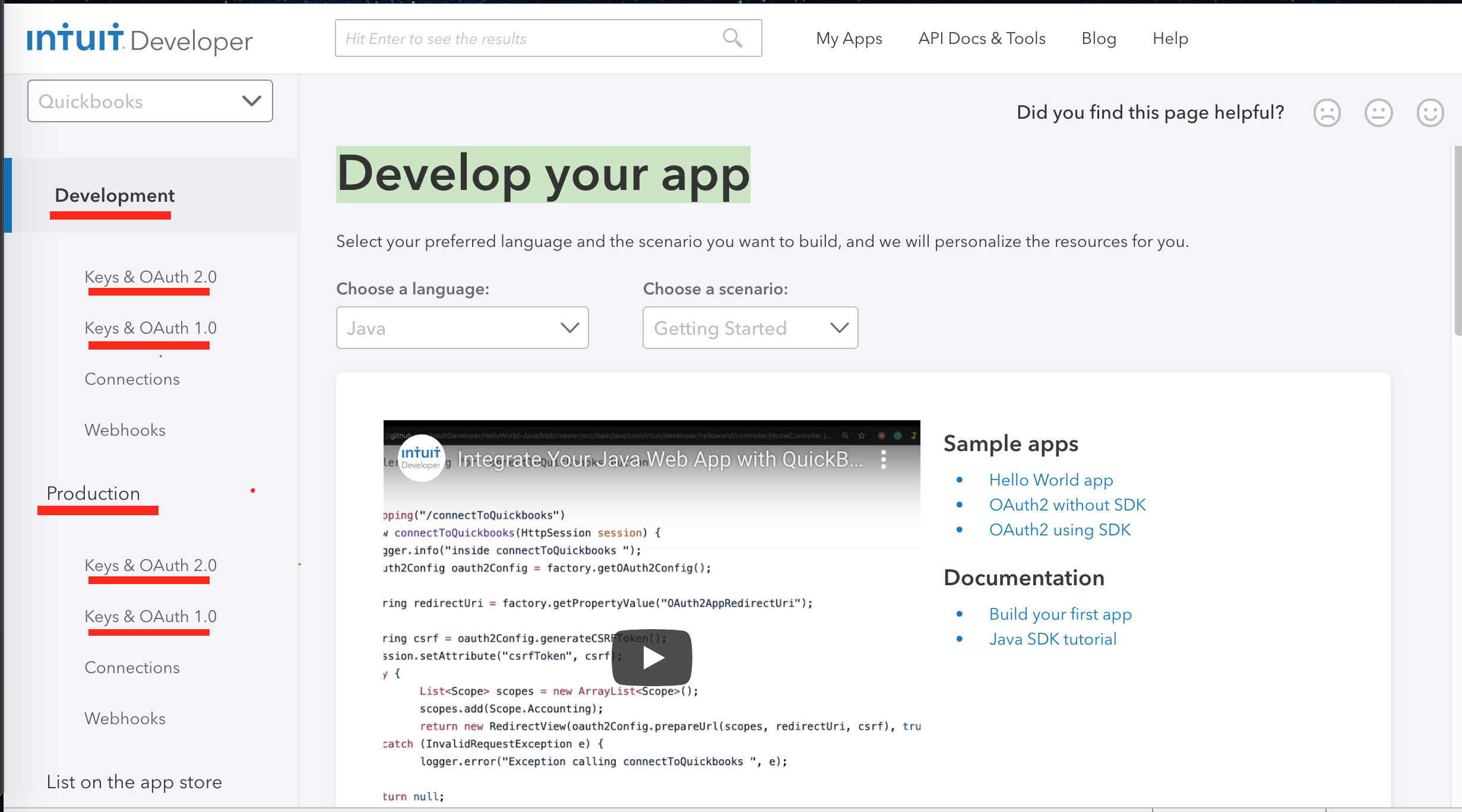
- Ensure you are using the proper key type, Development vs Production. You want to use the matching key types based on your QBO app. So if the OAuth1 app instance is using Production keys you will want to use OAuth2 Production keys for the migration.
- Note the areas underlined in Red to find Keys
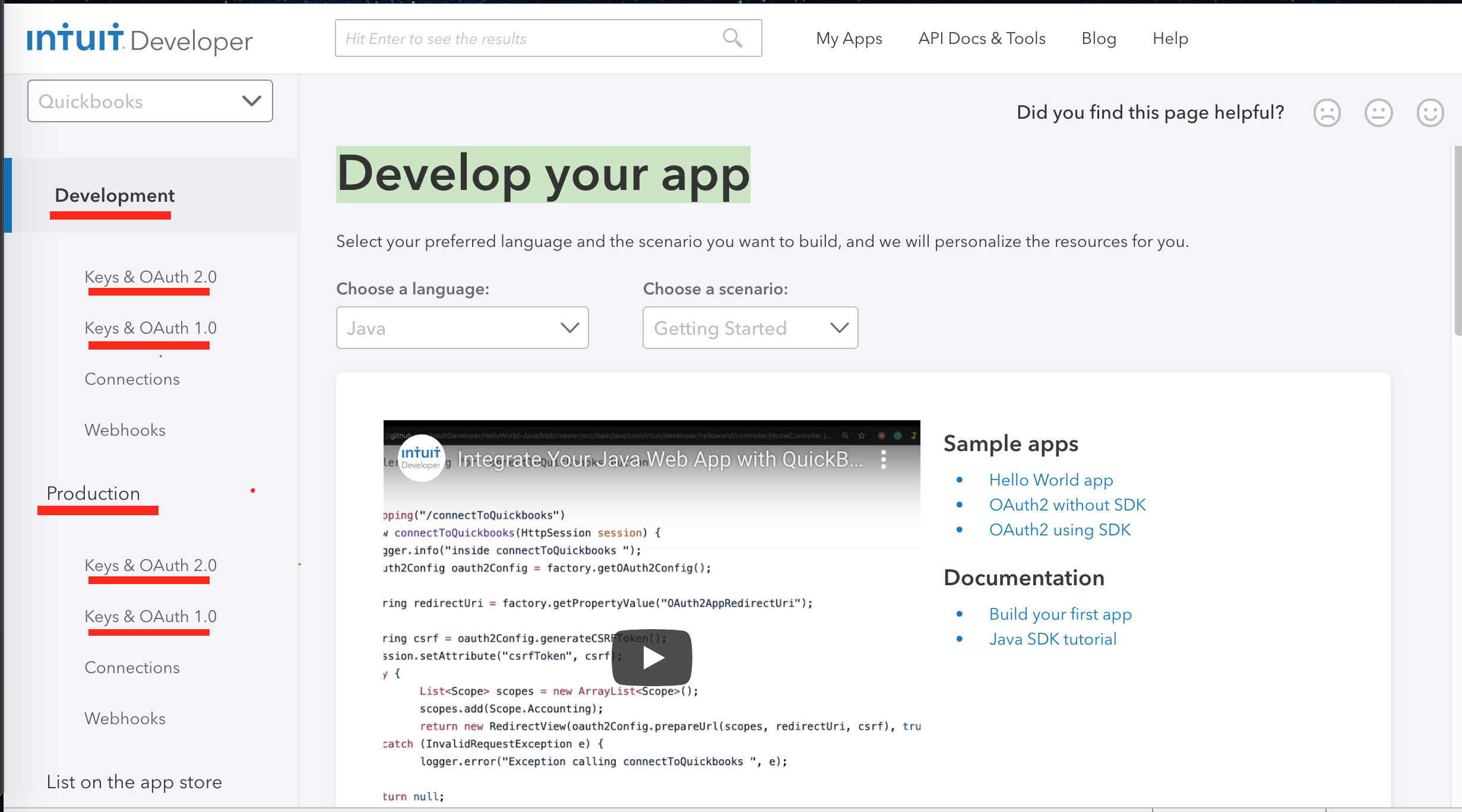
- Note the areas underlined in Red to find Keys
- The oauth.callback_url on the existing OAuth1 instance must match the Redirect URIs setup in the OAuth2 app.
- Quickbooks only accepts redirect urls that use HTTPS and does not support HTTP, therefore you will need to make sure the redirect url's in your QBO app are using HTTPS for any instance you want to migrate.
- Only valid OAuth1 tokens can be migrated to OAuth2 so if you have an invalidated instance returning 401s it must be re-authenticated prior to OAuth2 migration.